This Consumer Shopping Guide is designed to help consumers protect themselves from counterfeit and potentially hazardous toys, electronics, cosmetics and other popular products. This guide includes online shopping best practices, ways to protect financial and banking information, educational videos and infographics and general information to help you spot and report fake or stolen merchandise.
Special agents with Homeland Security Investigations work domestically and abroad to ensure consumers avoid purchasing stolen, counterfeit or illegally imported items.
Every year, the United States government seizes millions of counterfeit goods from countries around the world as part of its mission to protect U.S. businesses and preserve consumers' safety and health. From seizing fraudulent COVID-19 test kits, medical treatments and therapeutics, to preventing stolen catalytic converters from getting to market, to Operation Team Player’s seizure of nearly $97.8M in counterfeit sports merchandise in the year leading up to Super Bowl LVI, HSI is at the forefront of keeping consumers safe.
In addition to profiting from the sale of counterfeit goods, organized crime groups steal billions of dollars a year from unsuspecting American businesses and consumers, while draining tax revenue, destroying legitimate businesses and devastating our natural resources. Whether it’s through organized retail crime focused on selling stolen merchandise to unsuspecting customers online, or wildlife trafficking that results in the sale of illegal exotic animals, lumber or wooden household goods, these crime groups are relentless in their pursuit.
Crime prevention starts by being vigilant and knowing how to protect yourself and your family.
Shopping Tips
There are several steps you can take to protect yourself when shopping online:
- Purchase goods only from reputable retailers and be wary of third-party vendors.
- Check seller reviews and verify the seller's phone number and address in case you have questions about a product's legitimacy.
- Read product reviews on websites and research companies you're unfamiliar with.
- Don’t buy expensive items from third-party websites.
Remember: If a deal seems too good to be true, it probably is. Criminals use legitimate product photos on their websites, despite selling fraudulent products. Often, consumers pay full price for subpar items that don't last long.
Buying illicit goods impacts American innovation and erodes the competitiveness of U.S. manufacturers and workers—but the biggest danger illegitimate products pose is that they aren’t manufactured according to U.S. standards and codes.
Holiday and Sale Shopping Safety Tips
- Take advantage of security features. Passwords and other security features add layers of protection if used appropriately.
- Check privacy policies. Take precautions when providing information, and check published privacy policies to see how a company will use or distribute your information.
- Check your statements. Keep a record of your purchases and copies of confirmation pages, and compare them to your bank statements. If you find a discrepancy, report it immediately.
- Be careful about the information you publicize. Scammers may be able to piece together information from a variety of sources. Avoid posting personal data in public forums.
Top Counterfeit Products
Current Trends
- An increase in the use of e-commerce platforms and social media to sell counterfeit goods: The internet allows people from all over the world to engage with each other. It's opened the door for small and large businesses to reach customers they wouldn't have reached 30 years ago. Unfortunately, criminals and bad actors take advantage of the same mechanisms to target victims and hide behind the anonymity the internet provides.
- Third-party payment processors: While these companies have made it easier for smaller businesses to accept credit cards and bank transfers, criminals have found ways to abuse and take advantage of the same technologies.
- Shipping loopholes: Criminals and their networks often break up bulk shipments into smaller batches to limit the risk of loss, which increases customs officials’ challenges in detecting contraband.
- According to The Toy Association™, Inc: Sixty-six percent of parents now report that social media and digital content (such as streaming services and online gaming) influence the types of toys their kids want, which translates to new types of licensed toys inspired by favorite influencers and programming. It can be tempting for parents and caregivers to buy a hot-ticket toy at a cheaper price from online sellers they aren’t familiar with, but these types of deals are usually too good to be true; you may even purchase a counterfeit toy that doesn’t meet U.S. safety standards. The Toy Association also reminds gift-givers to be on the lookout for toys inspired by social media trends, such as new types of fidget or sensory toys. Not every toy is created equal, so be vigilant and purchase only from reputable brands and sellers.
- Operation Boiling Point: In 2022, Homeland Security Investigations and its global retail and law enforcement partners launched this operation to put organized theft groups, or OTGs, out of business. These sophisticated criminal organizations profit from illegally obtaining goods that they later sell to unsuspecting consumers in online marketplaces. OTGs are known to profit from organized retail crime, cargo theft, and other theft- and fraud-related criminal activities. Organized retail crime alone costs Americans about $15 billion in lost tax revenue, not including lost sales taxes — more than shoplifting. The average American family pays more than $500 annually in additional costs due to this type of organized crime. Learn more about Operation Boiling Point and organized crime
- Operation Engine-Newity: Since 2009, the IPR Center has been working with the automotive industry to address emerging health and safety threats related to the illegal sale and distribution of counterfeit automotive, aerospace, rail and heavy industry-related components parts and equipment. Operation Engine-Newity represents a collaborative effort between HSI, CBP, the FBI and other agencies to address threats such as counterfeit airbags, brake pads, steering rods and bearings.
- Operation In Our Sites: Operation in Our Sites (IOS) is a strategic offensive targeting the distribution of counterfeit products through websites. IOS counters online criminal activity by disrupting and dismantling organizations through criminal investigations, domain name seizures, and asset seizures and arrests. These actions target individuals operating illegal websites and those using legitimate websites to conduct criminal activity.
- Operation Body Armor: Operation Body Armor targets the illegal importation of unapproved, counterfeit or adulterated personal healthcare and beauty products into the United States. As online sales have skyrocketed, incidents of illegal product importation have dramatically increased. Several federal government agencies have joined forces with the health and beauty industry to combat smuggling and safeguard U.S. consumers.
- Operation Surge Protector: The prolific use of consumer electronics and technology products generated an opportunity for criminals to create and sell counterfeit devices. These products are often manufactured with substandard materials and without testing or passing safety requirements, posing a real public health and safety risk. The IPR Center coordinates Operation Surge Protector to stop the criminal trade of electronic components and devices that can malfunction and cause serious injury.
Investigative Efforts
Partners & Resources
- The Toy Association, Inc.
- Underwriters Laboratories | Be Safe Buy Real
- CBP.gov | The Truth Behind Counterfeits
- Consumer Product Safety Commission
- ICE.gov | Counterfeit Goods: A Danger to Public Safety
- Automotive Anti-Counterfeiting Council
- Association for Home Appliance Manufacturers
- FBI
- FDA | Cosmetics: Consumer Resources
- Federal Trade Commission | ReportFraud.ftc.gov
Statistics
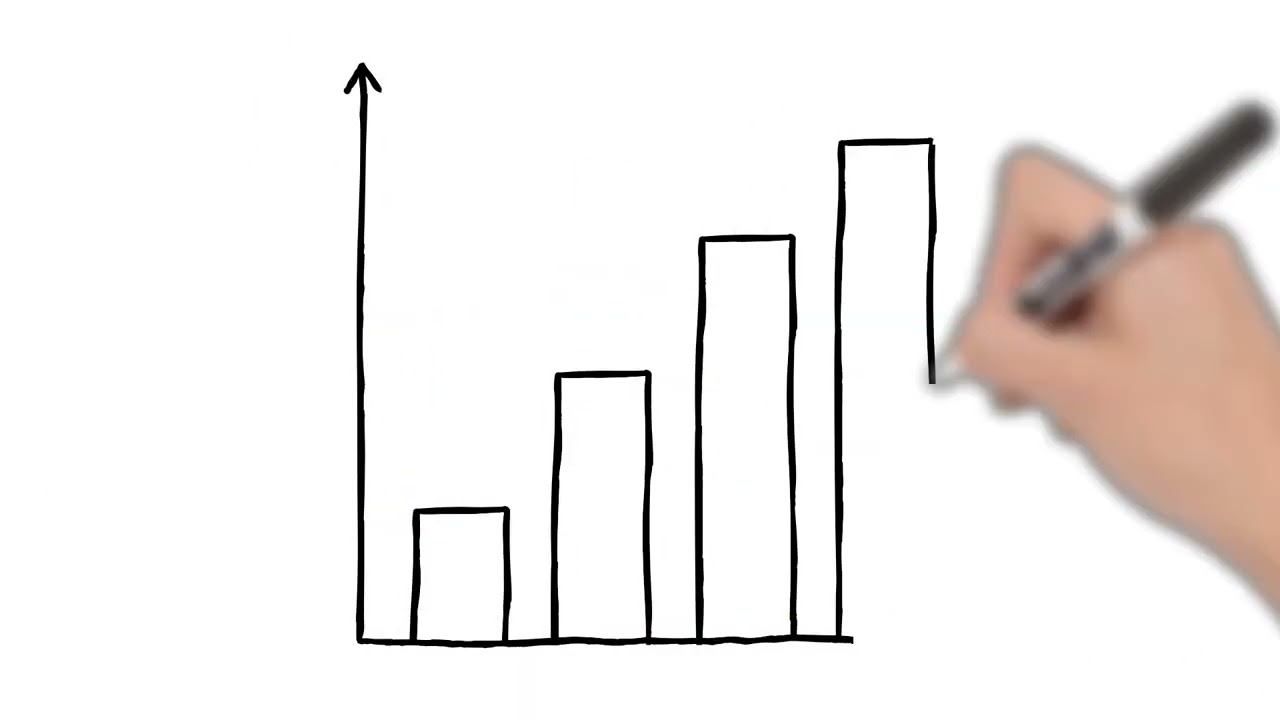
FY 2021 was another successful year for IPR enforcement, with CBP reporting more than 27,000 seizures with an estimated MSRP of more than $3.3 billion; that represents an increase of 152% over the previous fiscal year, when goods valued at $1.3 billion MSRP were seized for IPR violations.
Do's & Don'ts
Consider opening a credit card account for online-use only. Keep a minimum credit line on the account to limit the amount of charges an attacker can accumulate.
Debit cards do not offer protection against identify theft. Because banks immediately deduct charges from your account, an attacker who obtains your account information may empty your bank account before you even realize it.
Use good password practices.
- Use a different password for each account.
- Use the longest password or passphrase each system permits.
- Develop mnemonics, or memory aids, to remember complex passwords.
- Consider using a password manager program to keep track of your passwords.
Forget security basics.
- Keep your operating system, browser and software up to date.
- Use and maintain antivirus software and a firewall.
- Use caution with email attachments and untrusted links.
- Watch for suspicious activity on your accounts.
Criminals try to trick holiday shoppers into buying substandard (and often hazardous) counterfeit goods. Counterfeit electronics can explode, bicycle helmets can shatter, cosmetics can harm your skin and holiday lights can catch fire. Be vigilant. Protect yourself and your loved ones, and share this webpage to spread awareness.